CCTV Systems
CCTV is one of the most flexible tools in loss prevention. Besides the benefits of capturing crime specific events, CCTV, when monitored professionally, can also expose dishonest workers and breaches of company procedure, which directly or indirectly, lead to shrinkage. Our CCTV system applications are available in either covert or overt formats, designed to ensure that individual client needs are catered for based on a qualified concept design. Our track record in reducing losses and pin-pointing dishonesty, point of sale transgressions, external pilfering and shoplifting will give you the peace of mind that you require regarding your business security.
Our holistic professional approach to camera systems services, also guarantees that our cctv equipment is utilised to their full potential, providing you with the flexibility to focus on your hot spots within your organisation at any given time.
- Covert surveillance cameras
- Overt video surveillance system
- Off-site monitoring services
Transpeye
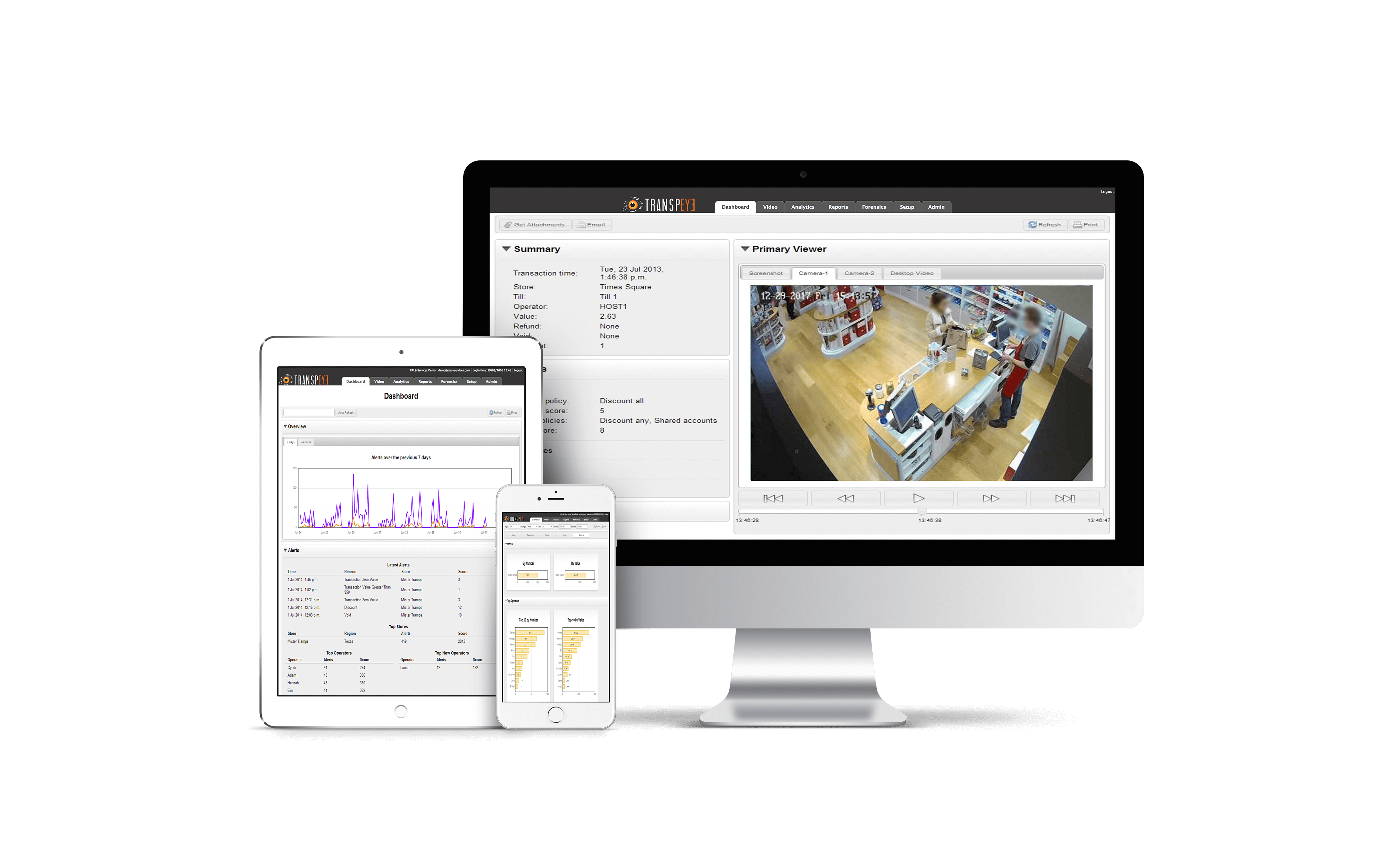
Transpeye allows the most efficient hardware and software smart combinations to maximise RISK management needs efficiently, ensuring the 1% of cctv camera systems required for observation is provided by exception.
Combining Transpeye with a CCTV camera system, security hardware and multiple data sources immediately adds value to your security investments to enable an efficient risk management solution where all system features are maximised and visuals reported via a dashboard with full reporting suite.

EPOS Integration combined with a CCTV camera system
Monitor EPOS based risks for internal and external fraud on an all in one combined system. The ultimate in efficiency! Set multiple risk based policies for any data, including Refunds, Voids, No Sales, Discounts, Training or any combination of these – to be alerted when one of those occur anytime, anywhere

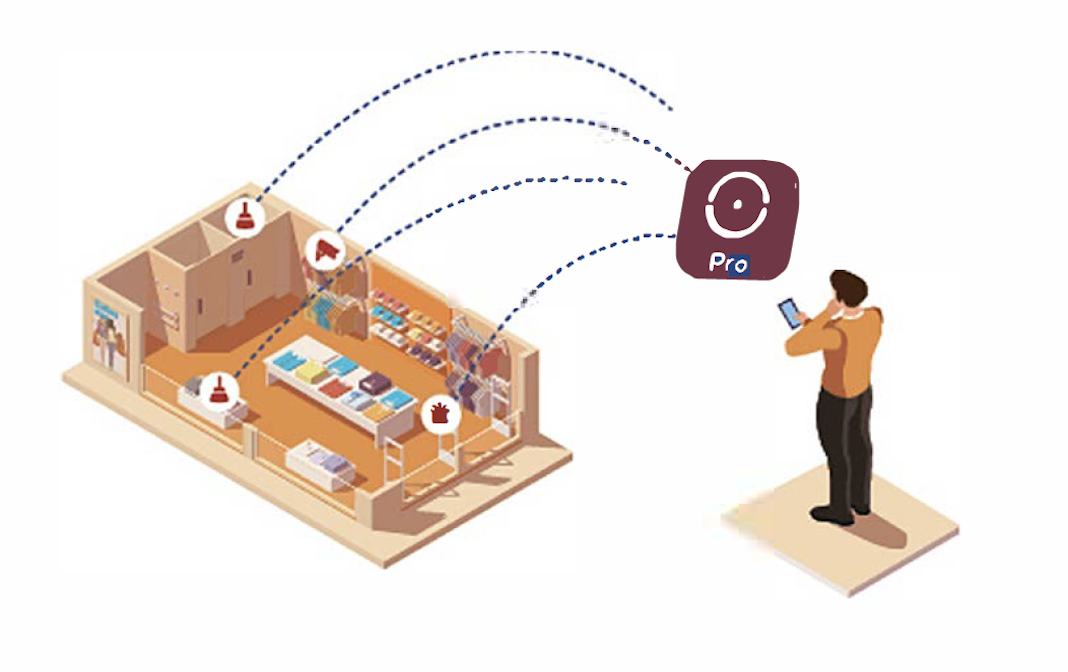
Smart Shelf installation connected to a camera system
Set Transpeye to notify on shelf selections of any QTY for any high risk product. Set low risk scores to notify with 1’s, 2’s or 3’s or really high scores for selections of 4’s or more to avoid shelf swipe and offer the best in customer service. Monitor with EPOS transactions for the ultimate in product protection.
Intruder Alarm Integration
Be alerted to alarm set and unset outside of expected routines / policy. Randomly check company policy compliance for entrance and exit. Ensure safety of team members. Manage risk of malicious and non-malicious activities for internal team access.
Full range of security cameras and DVR’s
Cctv installations are based around different features and different types. From Ultra HD Night Vision to panoramic cameras that cover the entire spectrum. What is the best option for determining your budget or your needs? Please see CCTV price information.
HD CCTV cameras
HD CCTV cameras offer clear, crisp pictures that allow you to spot suspected or abnormal activity easily. With higher resolutions like 1080p and 4K it’s easy for law enforcement professionals who need more detail in their investigations than what is offered by traditional security systems can provide them with.
Night vision cameras
NightVision cameras use infra-red lights to give you clear images even when it’s dark outside. Most importantly, these devices have night vision that is much better than what most people think of as “good” or standard quality – take advantage by contacting us if this interests you!
360 degree cameras
This camera is the perfect option for when you want to take pictures no matter what’s going on around it. You can record everything in a 360° panoramic view and still get high-quality photos with all of those pesky rain clouds or foggy mornings
The best quality CCTV camera installers in South Africa
At Lodge Security, we understand the importance of feeling safe and secure in your own business. That’s why we only use the best CCTV camera installers in South Africa. With years of experience and up-to-date knowledge of the latest security technology, our team can provide you with the peace of mind you deserve. We understand that every business is different, and we will work with you to tailor a security solution that meets your specific needs. Contact us today to learn more about how we can help keep your business safe.
Wired vs Wireless CCTV Options
If you are considering installing a CCTV system you will have to choose between Wireless/Wireless. The difference between them depends on how much it will cost.
Wireless CCTV options
Wireless CCTV systems make use of wireless technologies that can transmit video stored in clouds. They connect via WiFi and require an Ethernet cable connection for power supply, but they’re more cost-effective than wired solutions!
DVR system
16 channels Dvr with a 256 MB SSD to record, save and view footage. Including a 22″ LCD display. 16 Channels 12 V power source, NB connection and connector.
Wired CCTV systems
Whether you have a large property or are looking for comprehensive security, wired CCTV security systems are an excellent choice. They are perfect for deterring and detecting intruders, as well as providing evidence in the event of a break-in.
Worried about the safety of your business?
Lodge Security is a trusted CCTV installation service that provides the latest in security technologies to help protect your business. We understand the importance of keeping your employees and property safe, and our team is dedicated to providing you with the best possible service.
With our cutting-edge CCTV systems, you can rest assured that your business is safe and sound. Our systems are designed to provide you with maximum protection, so you can focus on what’s important – running your business. Contact us today for a free consultation!
How Can We Help
If you require further information or further advice on your security requirements. Please contact our team today.